Email Investigations: The Epicenter of Security Analysis
The hard truth: Emails are full user identities

Introduction
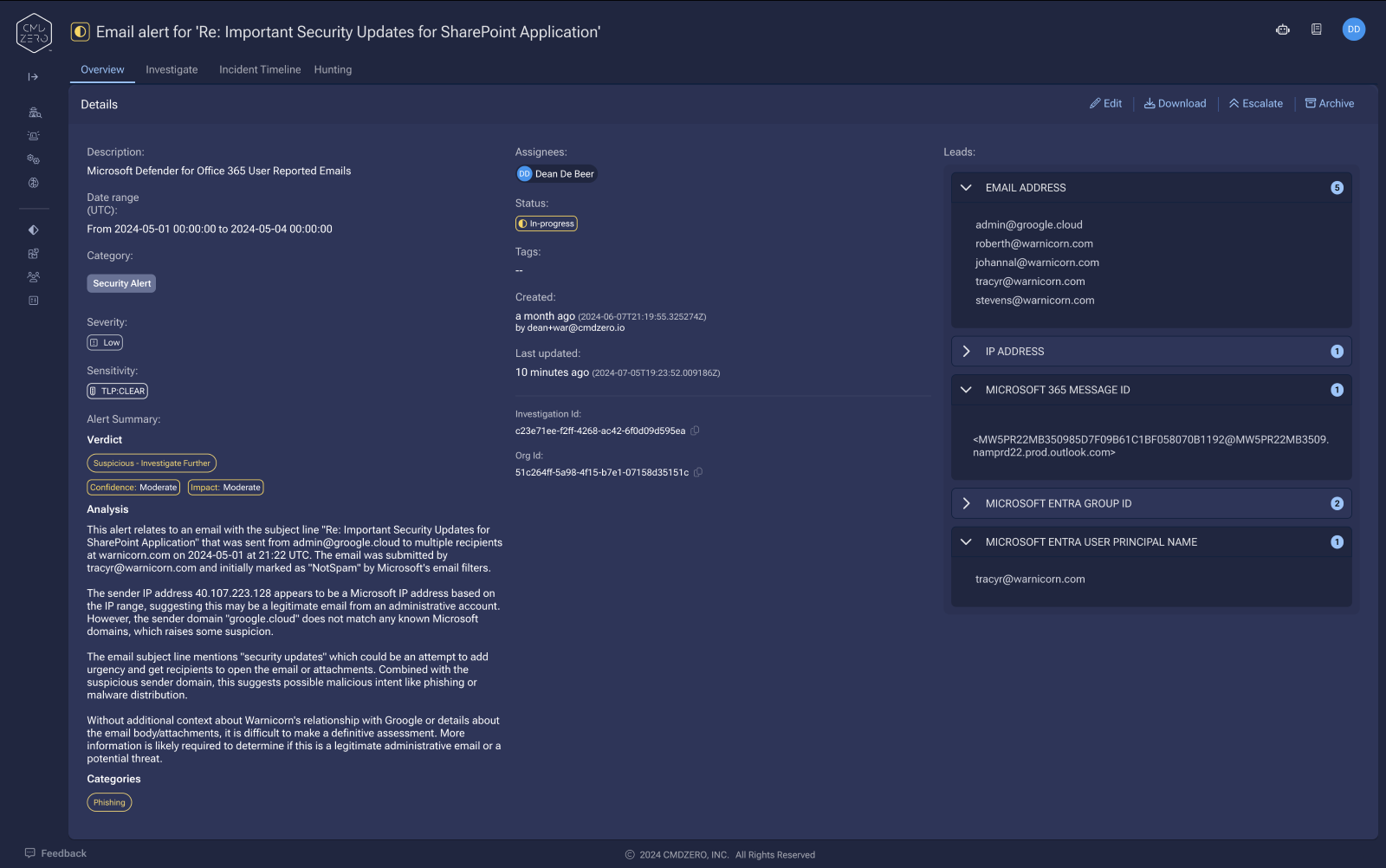
Email investigations intersect with virtually every security incident response. Whether it's an HR-led insider threat case or a potential compromise, email activity provides crucial context about what happened before, during, and after an event.
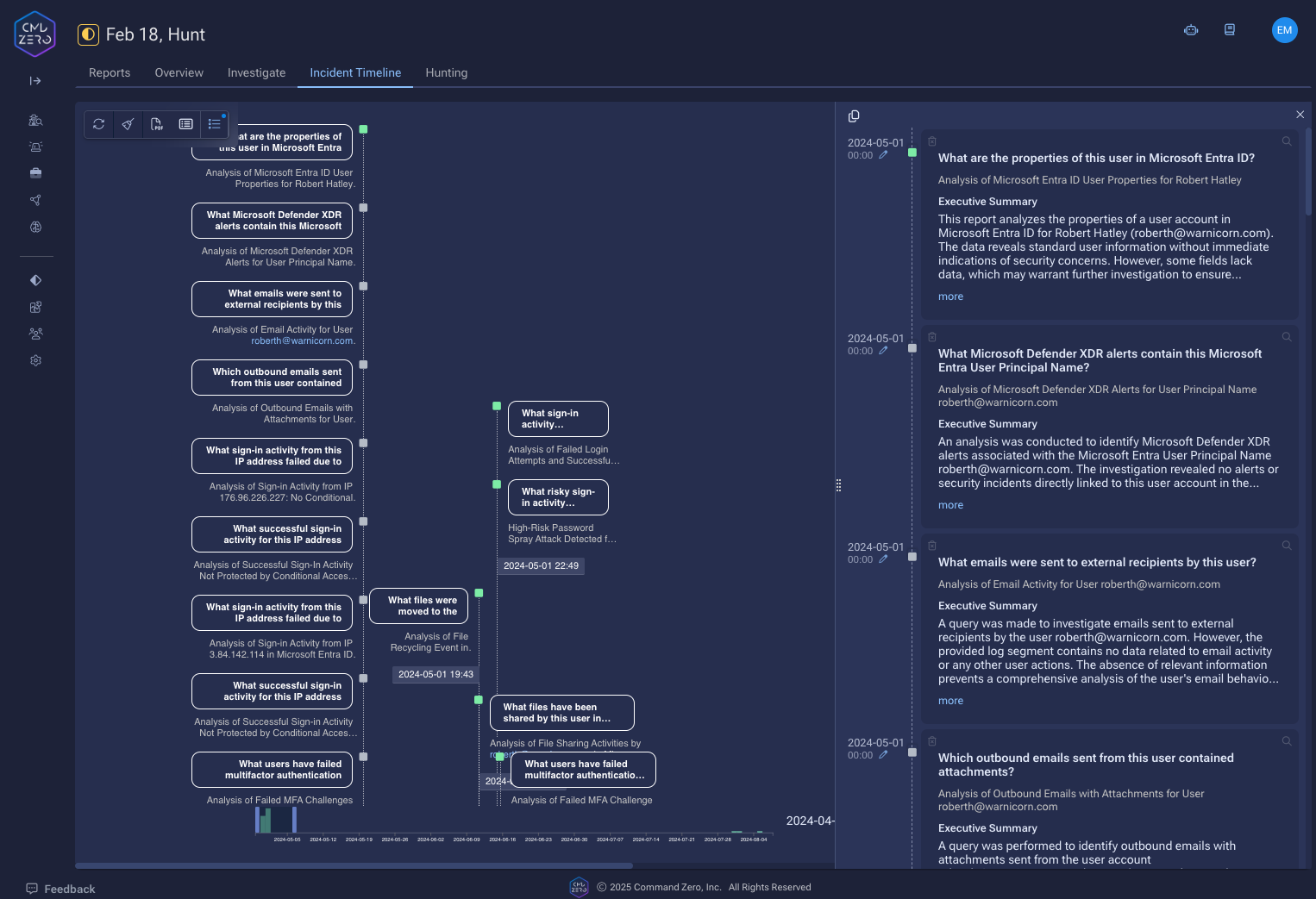
Most playbooks focus narrowly on whether a user clicked a malicious link, then jump straight to endpoint analysis. This misses critical signals in the user behavior. The noteworthy questions are: What did the user do in their email after the click? Did they start sharing sensitive files? Did they initiate unusual communications with accounts payable? How did their behaviors change in SaaS applications or other connected systems?
These post-compromise behaviors are nuanced. They often reveal the true scope of an incident, and they are easily overlooked by oversubscribed teams or static playbooks. More interesting patterns can be uncovered by asking questions like: Who else received these suspicious emails? What behavior changes did they demonstrate after receiving these emails or clicking the suspicious links?
These patterns can take hours to run down, so a complex email investigation can consume the majority of an analyst’s day.
The hard truth: Emails are full user identities
Email is one of the top threat vectors for a reason. It is used by every knowledge worker to interact with the outside world. In today’s integrated identity structure, email credentials represent more than just access to communications – they are full user identities. When compromised, attackers inherit all the permissions and influence of that account. So email compromise effectively becomes account takeover.
Take this real example: Examining the permissions of a user like Shannon at Acme Corp reveals extensive administrative access across multiple critical systems. Attackers can easily identify these high-value targets (admins with extensive access) through LinkedIn, derive their email addresses, and launch targeted social engineering campaigns. To cause devastating impact, attackers don't need to "spray and pray" across 50 users when they can focus on 2-3 privileged accounts.
Gaining access Shannon’s email gives attackers access to the keys of the kingdom.
Breaking down investigation barriers for email
Traditional email investigations face three key challenges:
- Speed vs. Accuracy Trade-offs: Thoroughly investigating email patterns while simultaneously checking other systems for signs of compromise requires significant time. An analyst needs to examine:
- Email subject line patterns
- Communications with external addresses
- Whether other internal users are participating in email dialogues with suspicious external addresses
- File sharing behaviors and patterns.
These manual correlations can consume the majority of an analyst's day.
- Access Complexity: Email investigations require pivoting across multiple systems. For instance, when investigating potential business email compromise (BEC), analysts need to quickly determine:
- What files were shared externally (via Microsoft Sharepoint, OneDrive or similar)
- Whether suspicious email forwarding rules were created (via Microsoft Exchange or similar)
- If the compromised identity has accessed sensitive systems through SSO providers like Okta or Entra (the two most prominent identity providers we see in customer environments)
- What SaaS applications the user can access via SSO (like GitHub or similar)
- Whether there's unusual activity in Microsoft Office365 or other cloud platforms
- Blast Radius Assessment: When an email account is compromised, security teams must rapidly determine the scope of potential damage. This means:
- Mapping access across multiple identity providers (both Azure AD and Okta)
- Understanding SaaS application access through SSO
- Identifying potential data exfiltration through file sharing or email attachments
- Assessing the user's permissions and group memberships
Modern email investigation requirements
Effective email investigations need to:
- Move beyond binary “received/didn’t receive email” or "clicked/didn't click malicious link" analysis to examine post-compromise behaviors
- Automatically correlate email activities with identity systems, file sharing, and SaaS access
- Provide guided investigation paths to help analysts explore relevant angles without going down rabbit holes
- Enable rapid assessment of potential blast radius when credentials are compromised
- Support complex use cases like BEC attacks, spear phishing, and insider threats
How Command Zero improves email investigations
Command Zero transforms email investigations through several key innovations:
- Unified Data Analysis: The platform abstracts data collection and interpretation across multiple sources, allowing investigators to pivot seamlessly between email, identity systems, and cloud platforms. This integration gives analysts immediate visibility into the full scope of potential compromise.
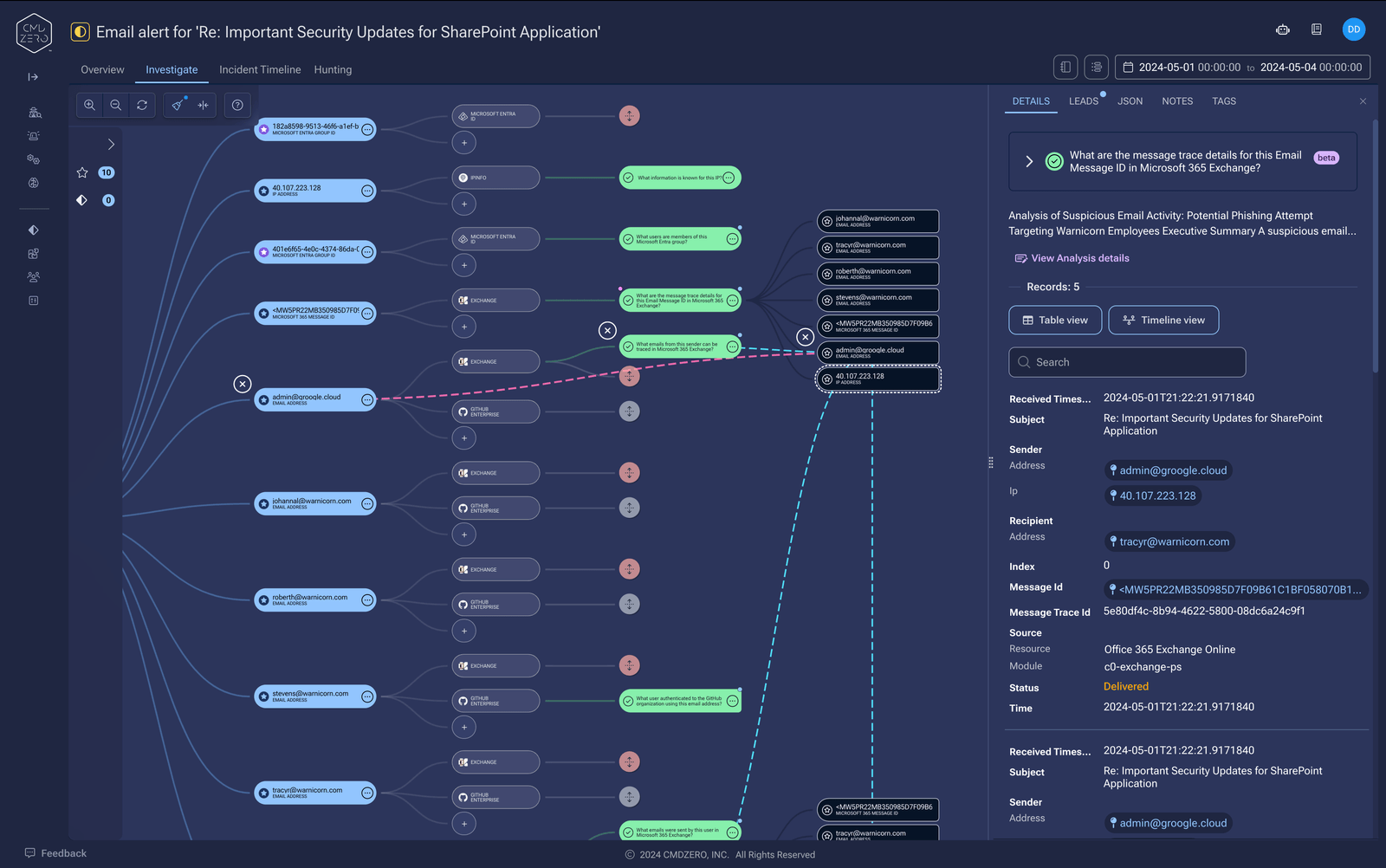
- AI-Guided Investigation: The platform's AI capabilities provide contextual guidance through:
- Recommended questions based on current findings
- Automated investigation paths based on responses.
- Guard rails that prevent "rabbit holing" into unproductive paths
- Context-aware follow-up questions that guide analysts toward promising leads
- Automated Timeline Analysis: The system analyzes events across all connected platforms and builds a comprehensive timeline. In roughly 95% of cases, investigations reveal no true security concern, but when they do, the system helps analysts rapidly understand the blast radius and pivot from "risk" to "active threat" assessment.
- Narrative Building: Command Zero helps investigators construct the incident narrative by:
- Pulling out key facts and correlations that might be missed
- Identifying connections between seemingly unrelated events
- Providing a structured approach to documentation
- Maintaining investigative guardrails to prevent scope creep
- Making sure that no pattern gets overlooked
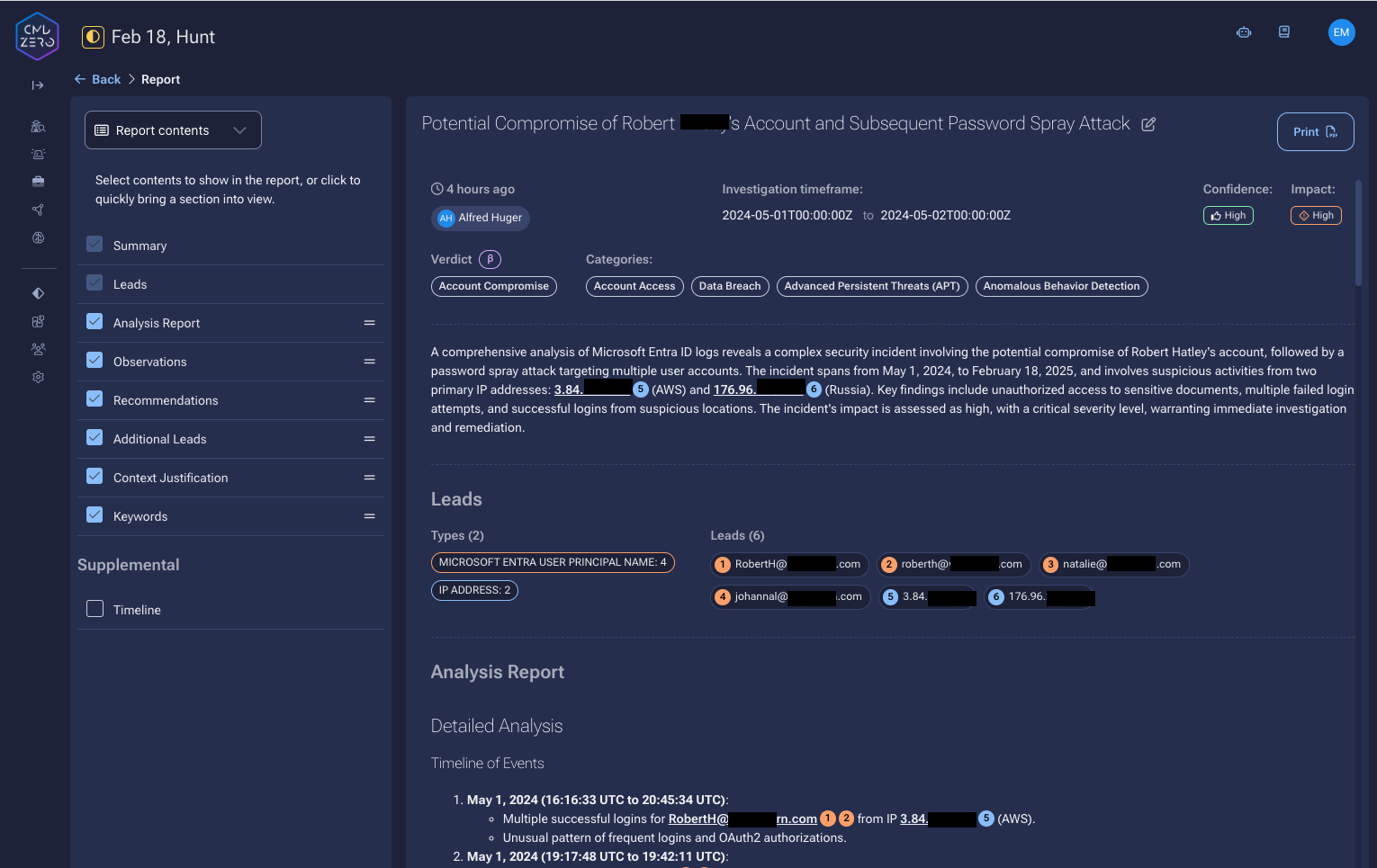
This approach differs fundamentally from traditional solutions by providing what amounts to an expert "riding shotgun" with the analyst. It decompresses the psychological burden on investigators by removing knowledge and access limitations, allowing them to conduct thorough investigations in minutes rather than hours.
Conclusion
Email remains the foundation of most security investigations, whether they involve business email compromise, phishing, or insider threats. Our experience shows that if an investigation doesn't touch email, it probably should - email behavior provides crucial context for almost every security incident.
Command Zero's approach transforms email investigations from a time-consuming manual process into a rapid, comprehensive analysis that any investigator can conduct effectively. By automating data correlation and providing expert guidance, we enable security teams to understand the true scope of incidents and respond decisively.
The reality of modern security is that email investigations can't be treated as a checkbox exercise. They require sophisticated tools that can handle complex data correlation while guiding investigators toward meaningful conclusions. This is how we turn the challenge of email investigations into an opportunity for more effective security response.
To see how Command Zero can help transform email investigations, please book a demo with our team.
Subscribe security updates
Run Better Investigations.
At Every Tier.