Investigate password spray attacks with accuracy and speed
What makes password spray attacks still dangerous in 2026?

Introduction
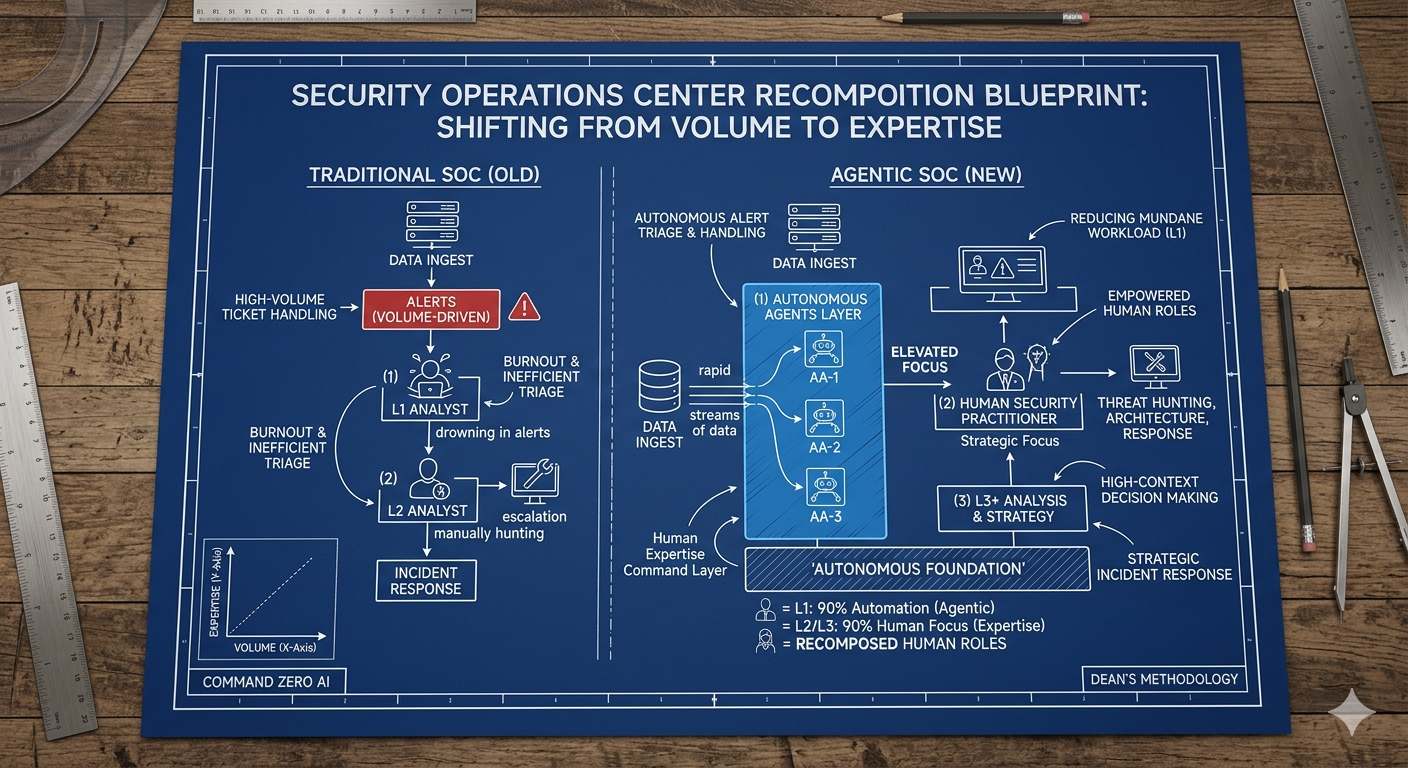
Password spray attacks are one of the most frequently investigated patterns on Command Zero by our customers, and they remain a persistent threat to enterprise environments. These attacks, while common, serve as a crucial barometer of an organization's security health. In this post, we will cover the critical role of password spray investigations for SecOps and how Command Zero is revolutionizing this important process.
What is a password spray attack?
A password spray attack is a type of brute force attack where attackers attempt to gain access to user accounts by guessing their passwords. These attacks can target a user or multiple users in an organization, they may try multiple passwords for a single account, a single password for multiple account or multiple passwords for multiple accounts.
Typical steps of password spray attacks
The attack typically follows the following steps:
- Attackers obtain a list of usernames, either by purchasing stolen credentials or creating their own list using common email formats and public information.
- They select a small set of common passwords, such as "123456" or "passw0rd"3. Or they re-use credentials available from dump material.
- Using automated tools, they systematically test these passwords across a large number of user accounts.
The process is repeated with different passwords until access is gained.
This method is effective because it exploits the human tendency to use weak, easily guessable passwords and often reuse them across multiple accounts. Password spraying attacks can avoid account lockouts and detection by limiting the number of attempts per account.
What makes password spray attacks still dangerous in 2025?
- The barrier of entry is low and they are cheap to run. Compared to more sophisticated attack types that require deep technical expertise, it is easy for an attacker to obtain or guess usernames and initiate password spray attacks. These attacks can be relatively cheap attacks to run as they only require minimal computation and an internet connection. That stated, password spray attacks are highly destructive. They accounted for 1/3 of all compromised accounts in 2020 (per Microsoft Entra ID’s data), it is fair to assume that they play a similar role in 2025. It’s no wonder password spray is one of the most common attack vectors targeting enterprises, possibly alongside phishing.
- Password spray can target thousands of users simultaneously. So, attackers can target seemingly unrelated sets of users in multiple organizations, increasing their probability of gaining access. These attacks are often automated and can occur over time to evade detection. It is easy for attackers to probe security policies to determine the best way to spray without being blocked or detected.
- Password sharing and default passwords for new users or default accounts are still common (even in 2025!). Attackers only combing the internet for these usernames and passwords still find some gold.
- Multi-factor authentication (MFA) and strong conditional access are powerful methods to prevent account takeovers, yet they may create a false sense of security. MFA and access policy exclusions exist in all environments, sophisticated attackers can bypass some of these controls within targeted attacks.
How to defend against password spray attacks?
To defend against password spraying attacks, organizations should follow the best practices: Implement multi-factor authentication, enforce strong password policies, and use account lockout mechanisms after a certain number of failed login attempts. Zero trust principles especially conditional access can prevent account takeovers and make password spray attempts more difficult for attackers.
Another essential defense is to investigate all password spray attempts thoroughly while auditing MFA and access controls. It is unlikely that our defenses will not be breached, but it is likely that we can minimize the damage by continuous investigations and immediate response.
The significance of password spray investigations
Password spray attacks are observed frequently in enterprise environments, and they offer valuable insights into an organization's authentication posture. When detected, they prompt several important questions:
- Is the attack targeting a specific high-value identity? List of identities?
- Have there been any successful breaches that went unnoticed?
- Does the attack indicate a potential data leak from a previous breach?
Answering these questions for each spray attack concern is crucial for maintaining robust security, but investigating spray attacks comes with its own set of challenges.
Challenges with traditional investigation methods
Investigating password spray attacks using native or standard tools can be a time-consuming and laborious process. Common challenges include:
- Time constraints: A single investigation can consume an entire day, adding hours to an already full caseload. This can result in analysts opting to investigate other cases, resulting in more exposure for password spray cases.
- Multiple system navigation and technical expertise: Analysts must move through various systems, from Entra ID to endpoints and collaboration platforms. Access to all these systems and the technical expertise required for thorough analysis are hard to come by.
- Superficial investigations: Due to time pressures, password spray investigations may be conducted superficially, creating a false sense of security. In this case, spray signals may be discarded as “non-issue”, potentially missing valuable patterns in the environment.
- Ever-changing alerts and security content: Major security vendors have strong security research teams providing content for their products. The content may result in high volume and ambiguity for analysis (this is especially true for Microsoft Office365 and Graph alerts). To stay ahead of new attack patterns, they modify existing alerts and publish new alerts - further complicating analysis.
How Command Zero transforms password spray investigations
Analysts can investigate password spray attacks using the pre-built questions and facets (pre-built investigation sequences) on a single platform, dedicated to tier-2+ analysis. This flow ensures that every password spray investigation can be completed in minutes with predictable outcomes.
Command Zero offers a solution that transforms the investigation process for password spray by:
- Increased efficiency: Using Command Zero, analysts reduce investigation time from hours to minutes per identity or case. The platform’s knowledge base is continuously updated to stay on top of changes in supported data sources. This relieves analysts from having to stay up to date with every update coming from data sources.
- Automation: Facets and pre-built investigations on Command Zero enable automated analysis, freeing up valuable cycles for analysts.
- Consistent and comprehensive analysis: Getting all patterns across data sources allows thorough investigation across multiple data sources without sacrificing other caseloads. This provides predictable flows, duration and outcomes for each investigation.
- Transparent Reporting: Command Zero provides clear documentation of the investigation process, enhancing accountability and training. Each step of the investigation can be reviewed for training, coaching and auditing purposes.
Key benefits for SecOps teams
By incorporating Command Zero into their workflow, security operations teams gain:
- Accuracy: Ensures thorough and precise investigations for each case.
- Speed: Dramatically reduces the time required for each case.
- Confidence: Empowers analysts to close cases with certainty.
- Consistency: Standardizes investigation processes across the team.
- Knowledge Sharing: Facilitates learning and collaboration among team members.
Conclusion
Command Zero's vision extends beyond password spray attacks. The platform aims to bring the same level of efficiency and thoroughness to all investigations, particularly in complex cloud environments with dozens of different data sources. As the threat landscape continues to evolve, Command Zero is positioned to help analysts tackle new and unfamiliar alert types with confidence.
Book a demo with our team to experience how Command Zero can help your analysts investigate password spray attacks and more.
Subscribe security updates
Run Better Investigations.
At Every Tier.