Introduction
Enterprise instant communication tools have long been considered a safe and controlled environment. Well, that is until attackers decided to target them with creative new attack vectors. Microsoft Teams—the backbone of enterprise collaboration—has become a primary attack vector for sophisticated ransomware campaigns targeting organizations worldwide. What began as isolated incidents has evolved into coordinated operations that exploit the intersection of technical vulnerabilities and human psychology.
The Mechanics of Modern Vishing
Modern Vishing targeting Teams isn't traditional phishing. We're witnessing engineered precision—a three-stage operation that weaponizes trust and manufactured urgency:
Email Flooding as Psychological Primer
Attackers initiate massive spam bombardments—hundreds of messages within minutes—creating operational chaos that primes targets for subsequent exploitation. Sophos MDR has observed more than 15 incidents involving these tactics in the past three months, with half of them in the past two weeks, indicating rapid acceleration.
Exploitation of Communication Trust Channels
The follow-up Teams call from the attackers appears legitimate and timely. Attackers present as IT support, demonstrating knowledge of the ongoing "problem" while offering immediate remediation. In documented cases, "As the [target] organization used a managed service provider for IT services, this did not set off red flags with the employee who accepted the [Microsoft Teams] video call [from an account named 'Help Desk Manager' from an external Microsoft 365 tenant]."
Remote Access Deployment and System Compromise
Through social engineering on the Teams call, attackers convince targets to install remote access tools—Quick Assist, AnyDesk, or TeamViewer. This provides complete system access, enabling malware deployment, credential harvesting, and lateral movement establishment.
Technical Architecture of the Exploitation
The attack succeeds by exploiting a critical Microsoft Teams misconfiguration that is common across Teams instances. Default settings permit external users to initiate communications with internal users—a configuration that organizations consistently fail to remediate.
Intelligence analysis reveals two distinct threat groups demonstrating sophisticated operational capabilities:
STAC5143: Advanced SharePoint Weaponization
One group – tracked as STAC5143, possibly related to FIN7 (though targeting orgs "smaller and in different business sectors than FIN7's usual victims") – tricks the targets into allowing a remote control session through Teams. They use this access to open a command shell and drop files and execute malware from an external SharePoint file store.
STAC5777: Legitimate Tool Subversion
The other group – tracked as STAC5777, and using techniques, tools, and procedures similar to those used by Storm-1811 – instructs the target employee to download Microsoft's Quick Assist remote access tool, and then proceeds to use the access to make configuration changes and deploy "a legitimate Microsoft updater with a malicious side-loading DLL that provides persistence, steals credentials, and allows for discovery of network resources." This group has successfully deployed Black Basta ransomware in documented cases.
Strategic Attribution and Scale Assessment
Multiple sophisticated threat actors are leveraging this mechanism: Black Basta Ransom Group, Storm-1811 Cluster, Midnight Blizzard, and Storm-2372. The rapid cross-group adoption indicates exceptional effectiveness and operational scalability.
The sophistication demonstrated—from precision-timed email bombardments to convincing technical impersonations—reveals that modern threat actors possess deep understanding of both technical vulnerabilities and human behavioral psychology.
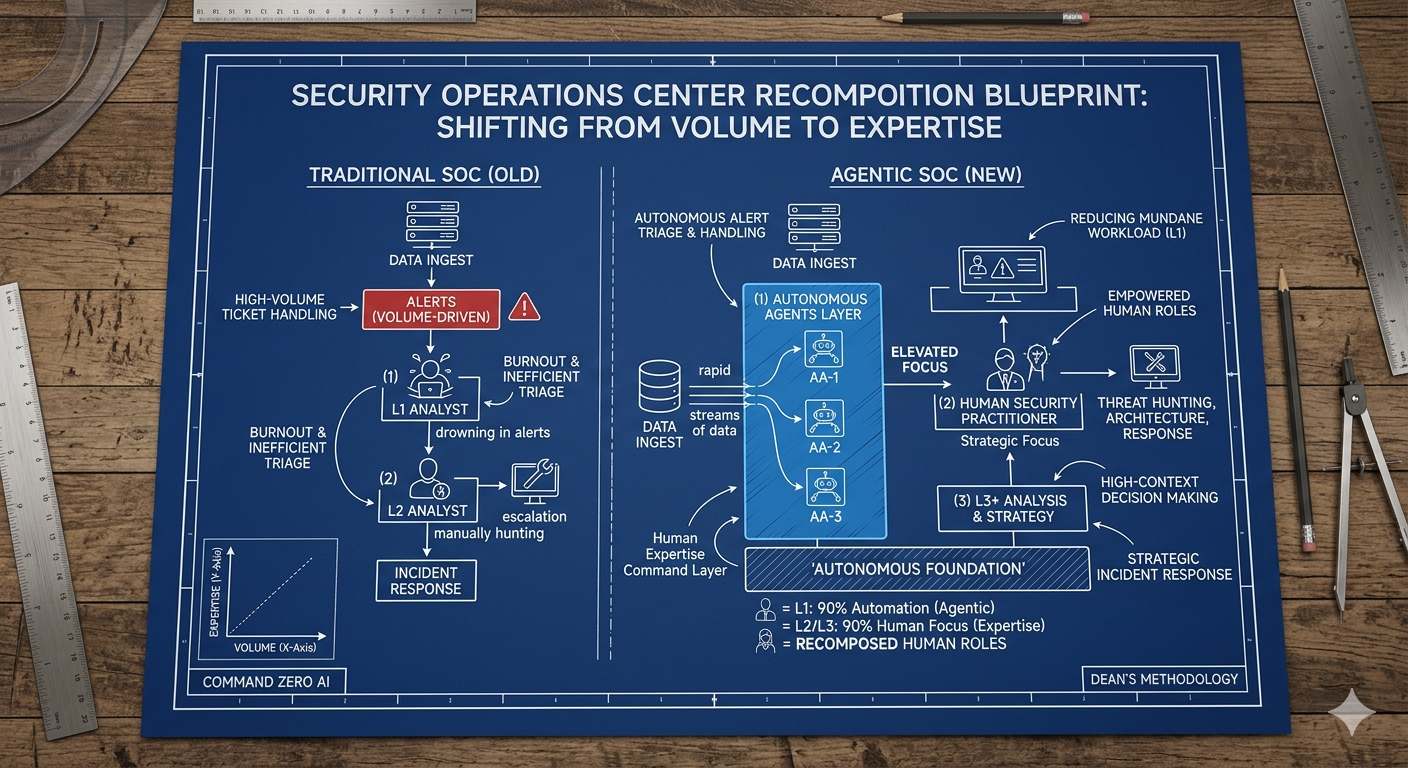
Command Zero's Strategic Response
Our post-Black Hat engineering initiative delivered comprehensive Microsoft integration enhancements, fundamentally expanding investigative capabilities across Microsoft Teams, Microsoft Entra, and Microsoft Graph environments.
Since August, the Command Zero platform provides unprecedented visibility into communication-based threats:
- Early-stage Attack Identification: New investigative queries designed to trace suspicious Teams calls, identify external callers impersonating IT support, and correlate call timing with email bombing incidents
- Remote Access Tool Detection: Enhanced visibility into Quick Assist, AnyDesk, and TeamViewer deployments, including installation timelines and correlation with suspicious Teams activity
- Lateral Movement Analysis: Advanced capabilities to follow the attack chain from initial Teams contact through network reconnaissance and credential theft
- Comprehensive Teams Security Assessment: Deep environment visibility enabling investigation of security incidents, HR cases, and operational auditing
These capabilities extend beyond security operations, supporting organizational requirements including compliance investigations and operational auditing—transforming how teams investigate complex, multi-stage attacks.
How to Defend Against Microsoft Teams Vishing Attacks: A Systemic Defense Framework
Organizations must implement comprehensive strategies addressing both technical architecture and human operational elements:
Technical Infrastructure Controls:
- Restrict external Teams communications to explicitly approved organizational domains
- Deploy application control frameworks preventing unauthorized remote access installations
- Implement advanced behavioral monitoring for suspicious communication patterns
Human-Centric Security Operations:
- Establish verified communication channels for all IT support interactions
- Deploy comprehensive social engineering awareness programs specifically addressing Teams-based attacks
- Create organizational protocols that validate support requests through independent verification
Strategic Implications for Security Operations
This campaign represents a paradigmatic shift in adversarial methodology. Threat actors are systematically weaponizing trusted communication infrastructures, exploiting psychological manipulation of manufactured crises, and leveraging default configurations that prioritize operational convenience over security architecture.
Organizations failing to address this hybrid threat model will continue experiencing compromise from increasingly sophisticated campaigns that blur the lines between technical exploitation and social engineering mastery.
Next Steps & Vision for Resilient Communications Security
As we continue monitoring this evolving threat landscape, our strategic approach remains focused on empowering security professionals with advanced investigative capabilities. The most sophisticated technical controls cannot independently protect against attacks that exploit fundamental human tendencies toward collaboration and assistance.
Command Zero’s philosophy centers on providing security teams with comprehensive visibility and actionable intelligence, enabling proactive identification of communication-based threats while supporting broader organizational security operations.
The future of cybersecurity operations demands solutions that seamlessly integrate technical detection capabilities with human behavioral understanding. Microsoft Teams vishing attacks represent just the beginning of this evolution—and we're uniquely positioned to address these challenges through continued innovation and strategic vision.
The question isn't whether your organization will face a Microsoft Teams vishing attempt—it's whether you'll be prepared to detect, investigate, and respond when sophisticated adversaries weaponize your most trusted communication platforms.
Book a demo today to see how Command Zero can help identify and analyze active threats in your environment.
Subscribe security updates
Run Better Investigations.
At Every Tier.